How to Set Up FTP Server on Ubuntu VPS
File Transfer Protocol (FTP) is a method for sharing files between computers over the internet using the TCP/IP protocol. It incorporates a client-server framework and Secure Sockets Layer (SSL) to ensure secure data transfer.
FTP is similar to the hypertext transfer protocol (HTTP) and simple mail transfer protocol (SMTP) but handles a different data type. It is essential for managing remote systems like a virtual private server (VPS).
In this article, we will explain how to set up an FTP server on an Ubuntu VPS. We’ll be using a vsftpd server, one of the fastest and most secure FTP servers for UNIX-like systems.
Prerequisites for Setting Up an FTP Server
Before getting into the steps, purchase an Ubuntu VPS hosting plan with extensive software support, like Hostinger’s, to avoid incompatibility issues. Note that your server must be running Ubuntu since the commands differ depending on the Linux distribution.
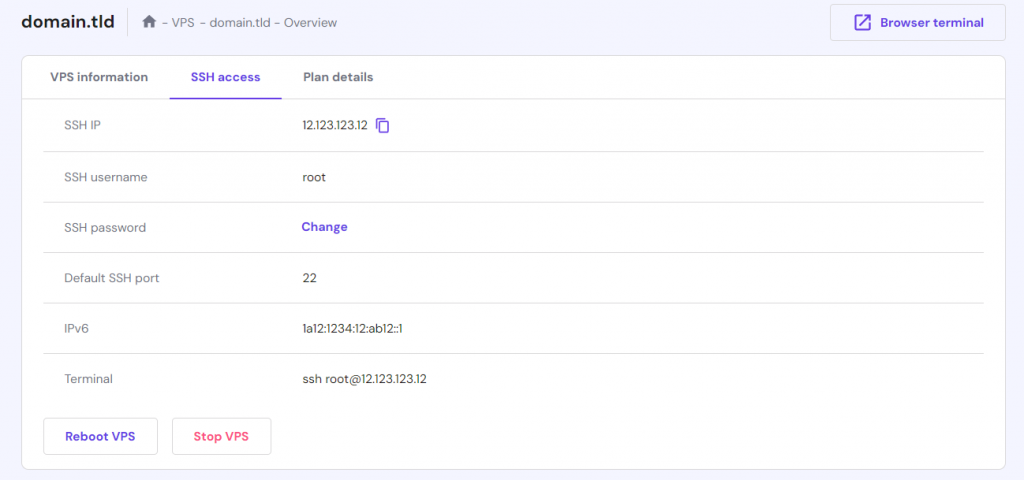
Then, connect to your server using an SSH client like PuTTY, Terminal, or Hostinger’s Browser Terminal. Hostinger users can find the IP address and login details under the SSH Access tab in hPanel’s VPS overview menu.
By default, you will connect as root. We recommend creating a new account with superuser privileges to avoid accidental destructive command execution. Here are the commands:
adduser account
usermod -aG sudo account
Replace account with your desired username. Then, switch to the new user by running the following command and proceed with the setup:
su account
cd
How to Set Up an FTP Server on Ubuntu
In this section, we will explain six steps to set up an FTP server on Ubuntu. If you find difficulty along the way, we recommend using the Hostinger VPS AI Assistant to help troubleshoot any issues.
1. Install vsftpd
Begin by installing vsftpd, which is responsible for enabling the FTP service on your VPS. Here are the steps:
- Download and install the package updates to ensure you get the latest vsftpd version. Run the command:
sudo apt-get update
- Wait until the update finishes and proceed with the vsftpd installation using this command:
sudo apt-get install vsftpd
- You will be prompted with a confirmation message. Type Y and hit Enter to continue with the vsftpd daemon installation.
- After the installation is complete, back up the original file so you can start with a blank configuration file:
sudo cp /etc/vsftpd.conf /etc/vsftpd.conf.original
2. Allow FTP Traffic from the Firewall
After installing, configure your system’s firewall rules to allow the Ubuntu FTP server to communicate via the internet. You can do so using the Ubuntu Uncomplicated Firewall (UFW). Here are the steps:
- Start by checking whether the firewall is already installed on your server using this command:
sudo ufw status
- If you see the ufw: command not found error, the Ubuntu firewall is not installed. Download and enable it by running the following commands subsequently. Skip this step if it is already configured:
sudo apt-get install ufw
sudo ufw enable
- Run this command to verify the firewall status:
sudo ufw status
- Once it’s active, run these commands individually to make sure FTP traffic is allowed:
sudo ufw allow OpenSSH
sudo ufw allow 20/tcp
sudo ufw allow 21/tcp
sudo ufw allow 990/tcp
sudo ufw allow 40000:50000/tcp
- Run the following command again to verify that you have added the new firewall rules correctly:
sudo ufw status
Check the Terminal output to ensure you have these ports open for the FTP server to work properly:
- OpenSSH is required if you wish to access your server via SSH. Sometimes, this option is enabled by default.
- Ports 20 and 21 for the FTP traffic.
- Ports 40000:50000 are reserved for the range of passive ports that will be set later in the configuration file.
- Port 990 allows TLS encryption when it is enabled.
3. Create the User Directory
After enabling communication for the protocol, create a new user that will use the FTP access. To do so, run the following:
sudo adduser hostinger
Replace the placeholder with your desired name. Then, enter a user password and fill in all the required details.
When configuring FTP, you should ideally restrict its access to one specific directory for security purposes. For this reason, vsftpd uses chroot jails to limit a local user to only their home directory by default.
However, vsftpd security might prevent non-FTP users from writing on their home directories. To solve this issue, create an FTP directory that acts as chroot, containing a writable folder for the transferred files. Here are the steps:
- Use the following command to create the FTP folder. Replace the account name accordingly:
sudo mkdir /home/hostinger/ftp
- Then, set the ownership using:
sudo chown nobody:nogroup /home/hostinger/ftp
- Remove the write permission:
sudo chmod a-w /home/hostinger/ftp
- Now, use the following command to verify the permissions:
sudo ls -la /home/hostinger/ftp
- The output should look like this:
total 8
dr-xr-xr-x 2 nobody nogroup 4096 Oct 8 11:32 .
drwxr-xr-x 3 hostinger hostinger 4096 Oct 8 11:32 ..
- Next, create the directory to hold the files and assign ownership:
sudo mkdir /home/hostinger/ftp/files
sudo chown hostinger:hostinger /home/hostinger/ftp/files
- Finally, add a test file to the directory, which we will use to test everything later on:
echo "vsftpd sample file" | sudo tee /home/hostinger/ftp/files/sample.txt
4. Configure vsftpd
Next, configure vsftpd and the FTP access. In this example, we will allow a single user to connect using a local shell account. The two key configurations required for this are already set in the vsftpd.conf configuration file. Here are the steps:
- Open the vsftpd configuration file using the nano command:
sudo nano /etc/vsftpd.conf
- Check that the following settings exist:
# Allow anonymous FTP? (Disabled by default). anonymous_enable=NO # # Uncomment this to allow local users to log in. local_enable=YES
- Enable the write_enable parameter. To do so, uncomment it by removing the hash sign (#):
write_enable=YES
- Uncomment chroot_local_user and change the value to YES to limit FTP user access only to files within the allowed directory. In the file, there are two of these parameters, and you must do the same for both.
chroot_local_user=YES
- Next, add the user_sub_token setting in the local_root directory path at the bottom of the file. It will apply the configuration file to the current user and other accounts you add later:
user_sub_token=$USER local_root=/home/$USER/ftp
- Specify the number of ports at the bottom of the configuration file to ensure your FTP server can accept substantial connections. Your firewall rules must allow them:
pasv_min_port=40000 pasv_max_port=50000
- To improve security, allow FTP access only to users specified in the configuration file. To do so, add the following parameter at the bottom. Ensure you set the userlist_deny flag to NO.
userlist_enable=YES userlist_file=/etc/vsftpd.userlist userlist_deny=NO
- Once done, press Ctrl + X, Y, and Enter to confirm the file changes.
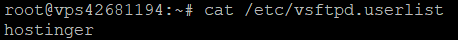
- After tweaking the configuration, create a user list and add your FTP account to the file. Run the following command in Terminal:
echo "hostinger" | sudo tee -a /etc/vsftpd.userlist
- Verify that the user is active by running the command below. Terminal should output the account name you added, which is “hostinger” in our case:
cat /etc/vsftpd.userlist
- Restart the FTP daemon using the following command to apply the changes:
sudo systemctl restart vsftpd
5. Secure the FTP Server
Since FTP doesn’t encrypt data by default, install an SSL/TLS certificate to secure the file transfer. Here are the steps:
- Issue an SSL certificate for the Ubuntu FTP server. In our case, we will make a key that is valid for 365 days and utilizes a 2048-bit private RSA key using this command:
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/vsftpd.pem -out /etc/ssl/private/vsftpd.pem
- Enter the corresponding personal details in the prompted field.
- After you finish creating the certificate, open the vsftpd configuration file again:
sudo nano /etc/vsftpd.conf
- Scroll down to the end of the file, and you should find these two lines that start with rsa. If they are uncommented, add the hash sign:
# rsa_cert_file=/etc/ssl/certs/ssl-cert-snakeoil.pem # rsa_private_key_file=/etc/ssl/private/ssl-cert-snakeoil.key
- Now, point the configuration file to the newly created certificate. Add the following directories below the two lines:
rsa_cert_file=/etc/ssl/private/vsftpd.pem rsa_private_key_file=/etc/ssl/private/vsftpd.pem
- Next, enable the SSL certificate and restrict the connection to only clients with an active certificate by adding this line:
ssl_enable=YES
- Then, add the following lines to reject anonymous connections over SSL:
allow_anon_ssl=NO force_local_data_ssl=YES force_local_logins_ssl=YES
- Enable the server to use TLS by adding the following parameters:
ssl_tlsv1=YES ssl_sslv2=NO ssl_sslv3=NO
- Next, disable SSL reuse to prevent FTP clients from breaking down and use high encryption cipher suites to set the key lengths to 128 bits or more. Do so by adding these lines:
require_ssl_reuse=NO ssl_ciphers=HIGH
- Save the file by pressing Ctrl + X, Y, and Enter.
- Finish by restarting vsftpd to apply the new configurations:
sudo systemctl restart vsftpd
Great work! You have now configured the FTP server on your Ubuntu VPS to work over the SSL/TLS protocol.
6. Test the Connection with FileZilla
The last step is to test whether your Ubuntu FTP server is working properly and securely. You can do so using an FTP client with encryption support. In this tutorial, we will use FileZilla.
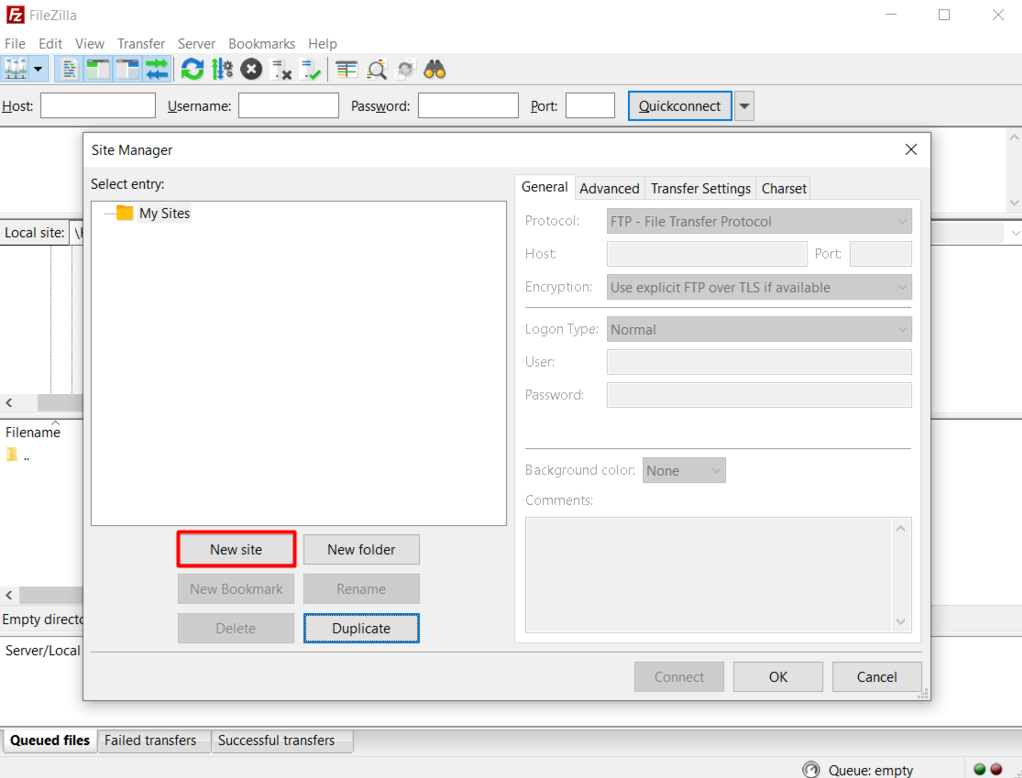
After you download and install the FileZilla FTP client in your local system, follow these steps:
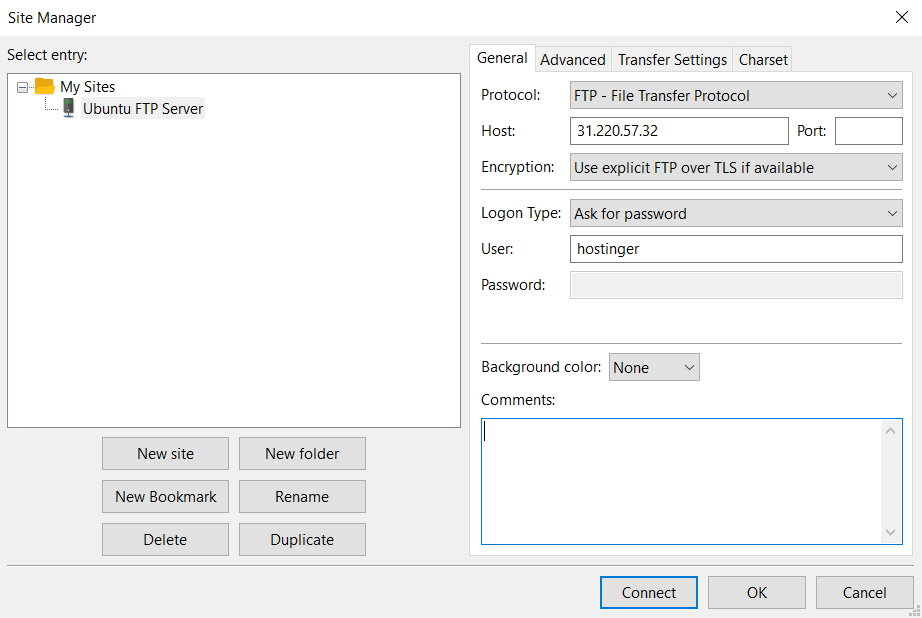
- Launch FileZilla and click on the Site Manager icon in the top right corner below File.
- A new window will appear. Click the New Site button and enter your Ubuntu FTP server details.
- Enter your newly created Ubuntu FTP server information in the corresponding fields. Since we configured it to use TLS, choose the Use explicit FTP over TLS option. The final configuration should look like this:
- Click Connect, and a screen asking you to enter the FTP user’s password will appear. Fill in the credentials and hit OK.
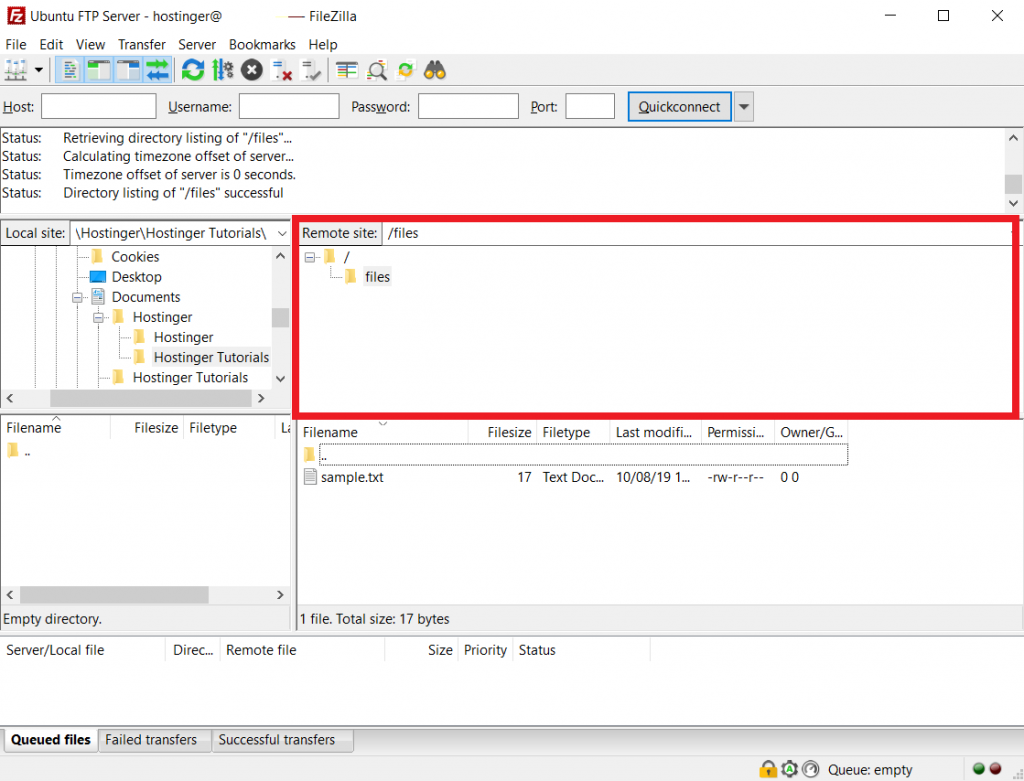
- Finally, verify the SSL certificate of your Ubuntu VPS FTP server. After confirming, the root directory with the test file should appear on your screen.
That’s all! Now, you can perform various file transfers from your computer to the Ubuntu FTP server and vice versa.
Conclusion
Setting up an Ubuntu FTP server simplifies file transfer between your remote server and local computer, improving development efficiency. In addition, it enhances security and ensures reliable connection by utilizing the SSL/TLS and TCP/IP protocols.
In this tutorial, we have explored how to set up an FTP server on an Ubuntu VPS using vsftpd in six steps. Here is a recap:
- Install vsftpd on your Ubuntu server and back up the original configuration file.
- Allow FTP connections through the firewall.
- Create a user directory accessible only for specified accounts.
- Configure the vsftpd settings.
- Secure the FTP server using SSL/TLS.
- Test your FTP connection with FileZilla.
Before setting up the FTP, remember to connect to your VPS via SSH and create a new superuser account. If you encounter difficulties during the process, use Hostinger’s VPS AI Assistant to help troubleshoot the issue quickly.


Comments
December 16 2018
Nice article! Thank you. Everything worked like a charm.
August 14 2019
Thank you very much for this article. It worked like it should and everything is explained well, kudos!
June 28 2020
Great article! It was very helpful - confirm all is working well on Ubuntu 18 VPS server and done via SSH terminal
July 07 2020
Happy to hear that, Bolat! :)
July 10 2020
This worked fine here, thank you
July 14 2020
You are very welcome, Udor! :)
November 02 2020
how do i move files out of the ftp folder? when i try to move the files out of the ftp folder it gives me permission denied
February 02 2021
Hi there, Rudy! If you're getting Permission Denied error, you're most likely not connected well to FTP. I'd suggest to re-check your FTP connection and make sure the correct port is allowed.
December 17 2020
Ubuntu 20 on VPS server, after your lesson Filezilla cannot connect to VPS - Error GnuTLS -15: An unexpected TLS packet was received. What's wrong? Thank you
February 09 2021
Hi there! This is most likely due to SSL being enabled on the server. Try encryption: Use explicit FTP over TLS ;)
September 17 2021
Hi! I am also getting this error: GnuTLS error -15 in gnutls_record_recv: An unexpected TLS packet was received. I tried with Use explicit FTP over TLS and also Require explicit FTP over TLS. Do you have an idea why this is happening? Thank you!
October 13 2021
Hi! It looks like your error comes after some time of inactivity. FileZilla and other FTP clients abort connections automatically after some time of no activity in order to save resources and prevent some type of DDoS attacks. Additionally, in the case of popular FTP clients - the FTP connections could clog quickly if inactive connections were not aborted. So all you'd need to do is make sure to make an action in FileZilla from time to time to keep the connection going.
October 19 2021
how to get host ip ?
October 19 2021
Hi, you can find your IP using the command:
ip aMarch 09 2022
Wow. That was an EXCELLENT step by step guide to installing a SECURE FTP SERVER on a VPS. Many thanks for your hard work, making it so easy for others to set this up.
March 09 2022
Happy to hear it was useful :)
April 13 2022
great article dude!
March 25 2023
Hello, Love the tutorial it is very straight forward and explains every step needed. After following your tutorial I still can't connect on FileZilla, port 22 is open and hostinger account is set, I can access the virtual machine on it. Status: Connecting to {ip-address}... Response: fzSftp started, protocol_version=11 Command: open "hostinger@{ip-address}" 22 Status: Using username "hostinger". Command: Pass: ************* Status: Connected to {ip-address} Error: Could not connect to server Any advice to fix this?
March 31 2023
Hello there! Make sure you got SFTP set up properly along with SFTP settings in /etc/ssh/sshd_config. I would suggest following this tutorial for more information. You can skip the Install SSH and Manage SSH Service parts since our VPSs already have SSH installed. If any issues occur, don't hesitate and contact our live support, and we'll gladly help you out.
July 31 2023
Hi, i am getting the following error when i try to connect: Error: GnuTLS error -15 in gnutls_record_recv: An unexpected TLS packet was received. Error: Could not read from socket: ECONNABORTED - Connection aborted Error: Could not connect to server i have require explicit ftp over tls enabled, how do i fix this error?
August 04 2023
Hello, try testing the connection with https://ftptest.net/. It will show if the issue is on your server or your device.
August 25 2023
Hello there, CyberPanel uses 8090 TCP port, so you might want to allow it. Also if you got a VPS at Hostinger you can simply reset the firewall to fix this issue. Alternatively, try disabling ufw all together to see if that helps.