What Is a DKIM Record? Everything You Need To Know
DomainKeys Identified Mail (DKIM) is an authentication method used to prevent email spoofing. It increases email security by allowing the receiver mail server to check the authenticity of the sender’s domain.
A DKIM record is a DNS TXT entry containing a public key for email verification by recipient servers. It comprises elements like a name, version, and key type, typically provided by your email service, to authenticate messages.
While nearly 85% of all emails go to the spam folder, DKIM can prevent your email from doing so by providing cryptography authentication. It also prevents hackers from altering your message in transit or forging your email account for malicious activities.

What Is a DKIM Signature?
The DKIM signature is a special header containing essential information added to an email message. The DKIM signature header is in a unique textual string format, also known as a hash value.
The information presented in a DKIM signature header field uses tag=value pairs. A tag is a single letter, followed by an equal sign, while the value gives specific details of the email sender, the message, and the public key location.
There are required tags that all DKIM signatures must have, as the verification process would fail without them. These include:
- “v=” is the version of the signature specification. The value is always one.
- “a=” reflects the algorithm of the signature. This value is almost always rsa-sha256.
- “d=” this is the domain name.
- “s=” indicates the selector record name, used with the domain name identity to locate the public key in DNS.
- “h=” specifies the list of headers used to create the hash data.
- “b=” represents the hash data.
- “bh=” illustrates the computed hash of the mail message.
Some optional tags are not compulsory in a DKIM signature but can help with providing additional security measures. These are the optional tags recommended in DKIM signatures to help identify spam:
- “t=” is the time of the message. The format is the number of seconds from 00.00.00 seconds on 1 January 1970 in the UTC zone. For example, if you send an email message on 7 May 2021, at 07:42:40 UTC, the “t=” value will be 1,620,373,360.
- “x=” this is the DKIM signature expiration time. Its format is the same as above, but the value must be greater than the time.
Note that the values of the optional tags are automatically generated, so there’s no need to calculate the seconds yourself.
How Does DKIM Work?
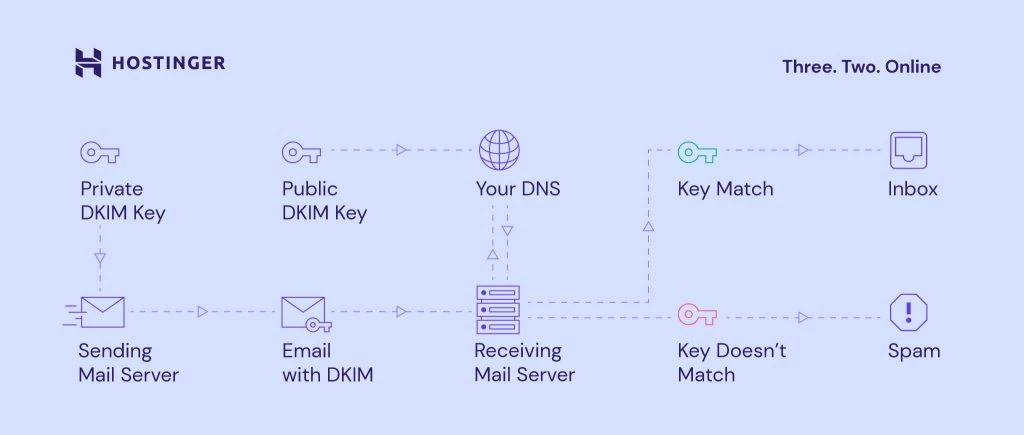
Before we show you how DKIM works, you should familiarize yourself with the concept of the two DKIM keys. These include the public key for the DNS record, which helps the receiving server to verify an email message, and a private key for your mail server as part of the authentication process.
All of the DKIM processes take place internally within the mail servers themselves.
For example, you are sending an email message using test@example.com. Before sending a message, the sending mail server will generate a DKIM signature header using a private key.
The mail system will start the DKIM verification by ensuring the DKIM signature matches the sender’s information.
When the message is delivered, the receiving email server will obtain the DKIM record from example.com’s DNS record. The receiving email server then uses the public key in the DNS record to verify the message’s DKIM signature.
If the public DKIM key matches the information in the signature, the message is proven to be authentic and will be moved to the inbox. This means that no one has altered the message in transit.
If the DKIM key doesn’t match the information, the message will most likely go to the spam or junk folder.
Is DKIM Related to SPF and DMARC?
DKIM is not the only security standard that protects your email messages. The Sender Policy Framework (SPF) and Domain-based Message Authentication, Reporting, and Conformance (DMARC) standards can also protect your email infrastructure.
SPF restricts those who can send emails from your domain, which protects it from spoofing. SPF is an email authentication protocol that ensures your domain only sends emails from a verified list of servers.
DMARC unifies the SPF and DKIM authentication methods into a common mechanism. DMARC also gives domain owners this mechanism to communicate how to deal with unauthenticated messages.
DKIM, SPF, and DMARC work on different authentication aspects, and they can support one another. Together they provide the best result for email security that will also increase domain reputation and email deliverability.
Is DKIM Really Important?
DKIM authenticates the email sender’s identity to ensure that messages don’t go to the spam or junk folder. It is essential for organizations that often send business emails or transactional emails to their customers.
Part of an organization’s or a business’s responsibility is to protect the integrity of its domain and messages. Without DKIM, hackers can easily send emails that might appear legitimate and potentially scam customers.
DKIM also helps to improve email deliverability as having authenticated emails helps increase the domain reputation among internet service providers (ISPs) and mail servers.
Suggested Reading
To enhance your email’s professionalism, explore our straightforward guides on setting up Outlook and using Gmail with your own domain name.
How to Add a DKIM Record for Emails
There are three basic steps to set up DKIM – generate the DKIM keys, enter a public key to the DNS server, and enter a private key to the sending email server.
Most email providers that support DKIM will generate the public key to add to the domain’s DNS record. For this, it’s essential to have access to your DNS record.
Some email services, such as Google Workplace, might generate the private key automatically, or you might have to add it manually.
In the next section, we will show you how DKIM works with different email services.
Adding DKIM Record Using Hostinger’s Email Service
Using an email service offered by web hosting providers can simplify the steps. With Hostinger’s email service, simply set up a Hostinger email, and Hostinger will automatically add the DKIM records.
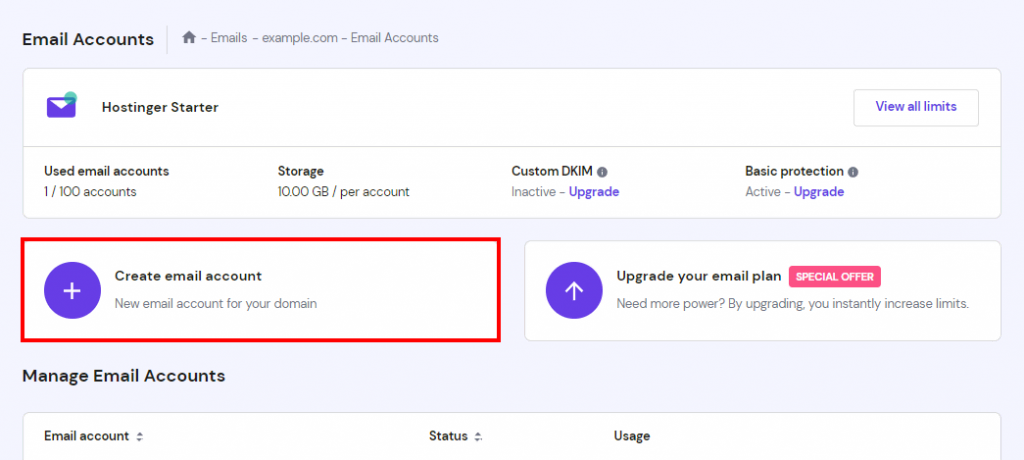
1. To set up new Email Accounts, log into your web hosting account and click on the Manage button next to your domain name. From there, head to Emails → Email Accounts.
2. Select Manage next to your domain name and click on the Create email account button.
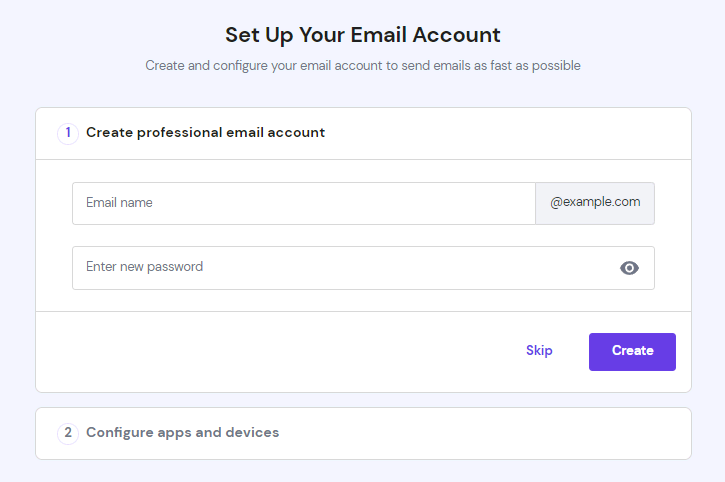
3. Fill out the form under Set Up Your Email Account, then click the Create button.
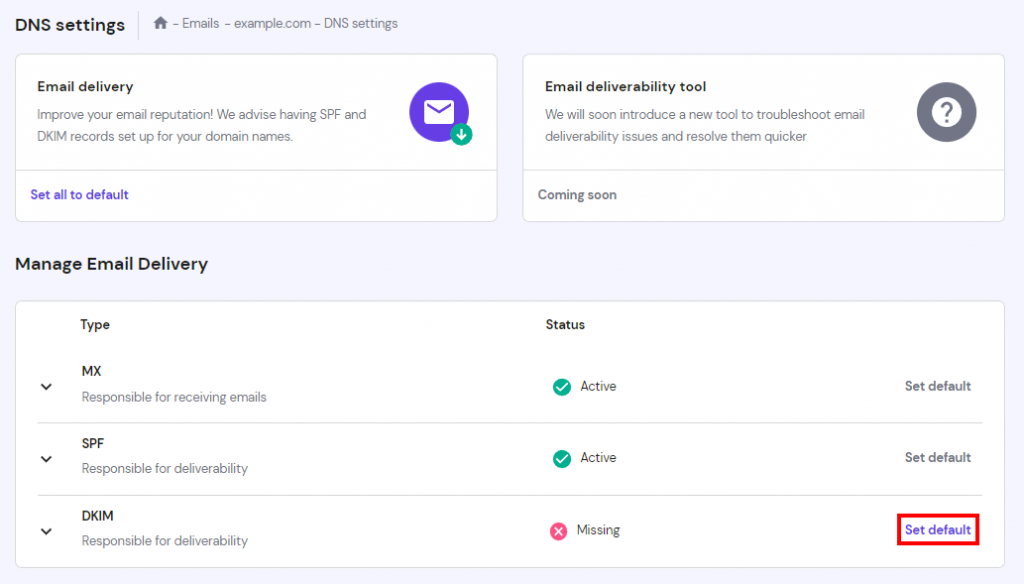
4. Head to DNS Settings and click on Set default next to DKIM. It will take up to 24 hours to propagate.
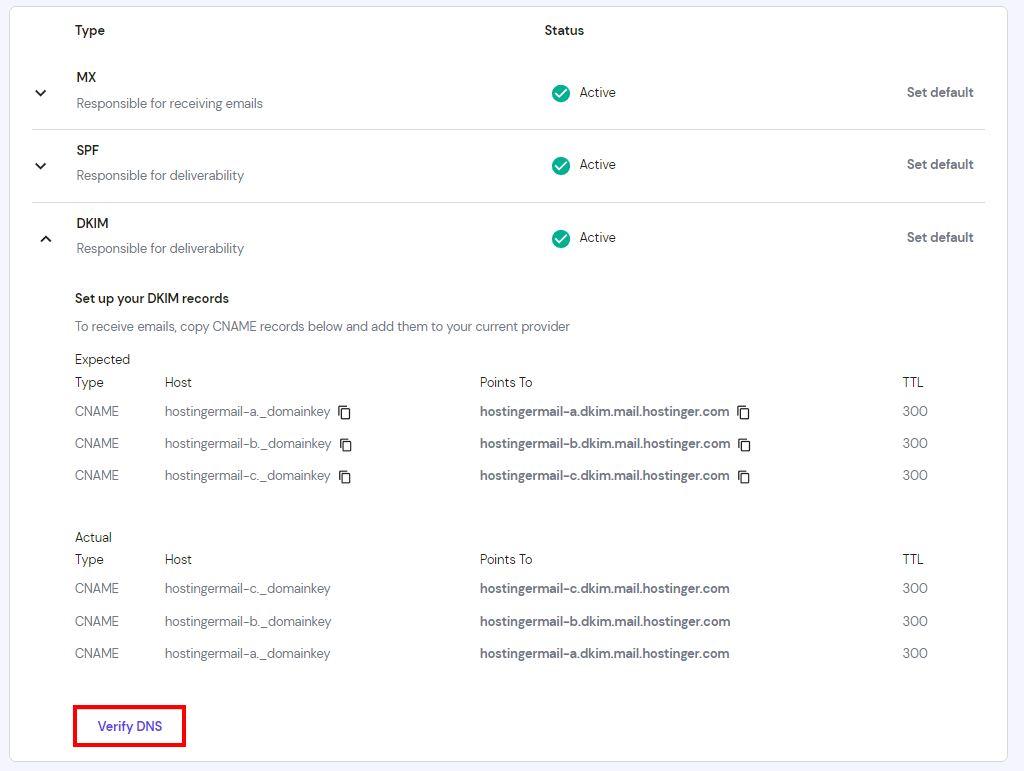
5. Once the Status has changed to Active, select the arrow icon next to DKIM and click on Verify DNS.
Adding DKIM Records From Other Email Provider
The main setup for DKIM is more or less the same with any email service provider (ESP).
Popular ESPs, such as Hostinger email or Google Workspace, have made it easy and fast for users to add DKIM records. For this section, we will set up DKIM using Google Workspace as an example.
Even though Gmail signs all email messages with the default DKIM domain key, it is better to manually authenticate your email domain for an additional layer of security.
Here are the steps to set up DKIM in Google Workspace:
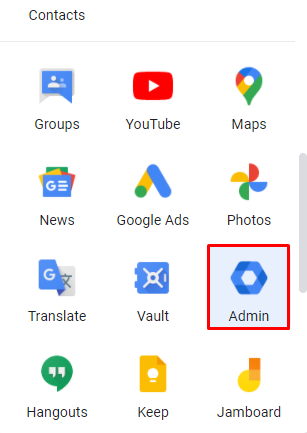
1. Log in to your Google Workspace account and select the Admin button under Apps. Note that access to the Admin console homepage is only available for Google Workspace emails.
2. From the Admin console homepage, click on the three lines on the header next to Google Admin. Head to Apps → Google Workspace → Gmail to start the authentication process.
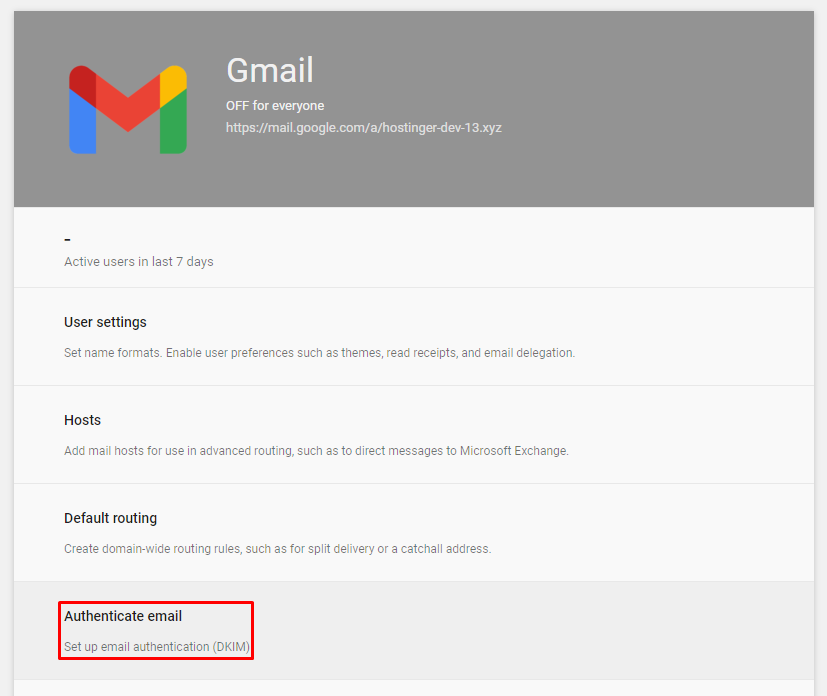
3. Click on Authenticate email to set up DKIM.
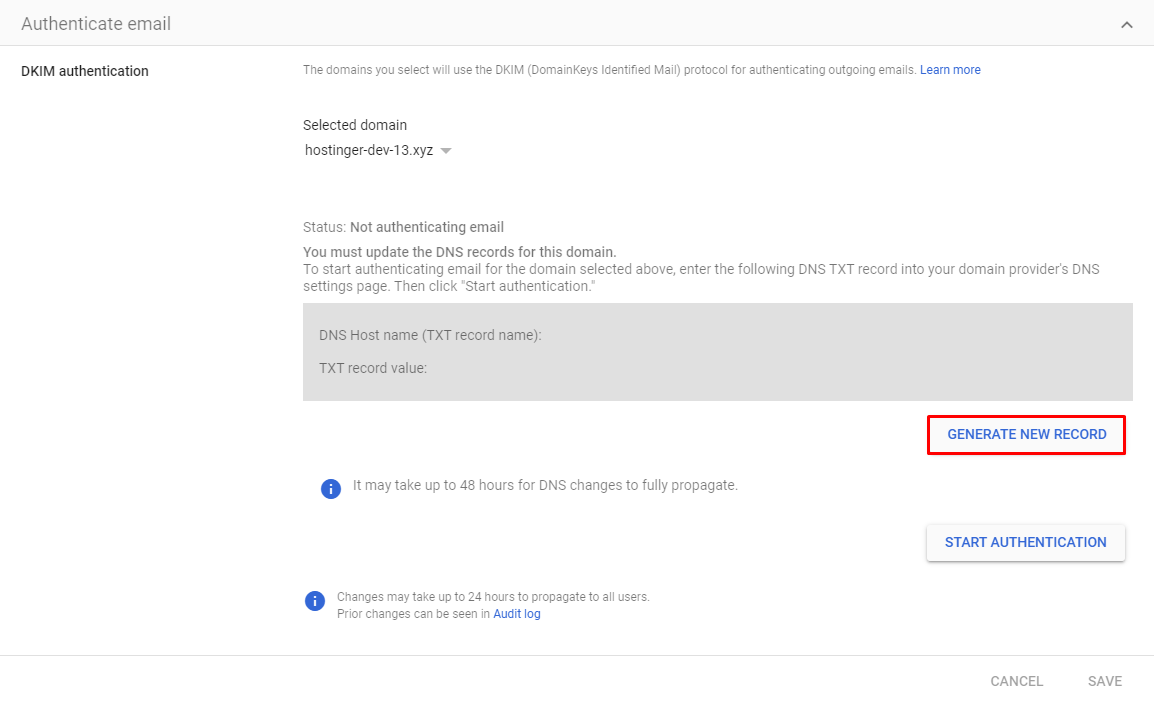
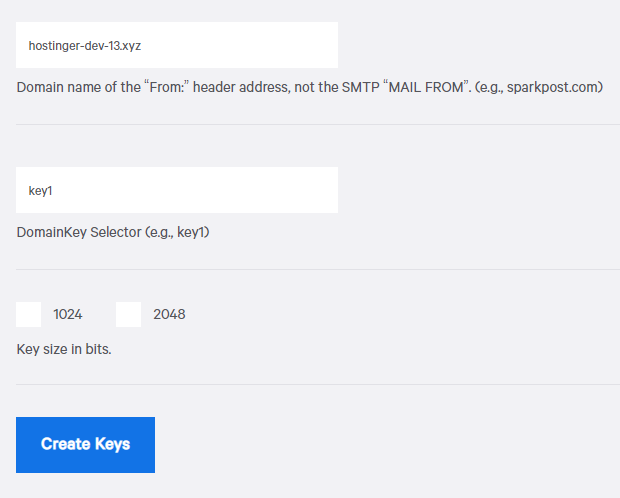
4. Don’t change the Selected domain as it will automatically be your domain. Simply click on GENERATE NEW RECORD.
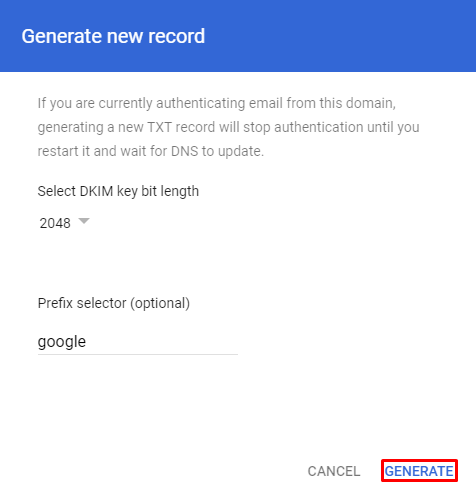
5. First, select the DKIM key bit length. We recommend selecting 2048 for a more secure option. Some domains only support a 1024-bit key, so make sure to check with your domain host. The Prefix selector can stay as “google”. Click GENERATE to proceed.
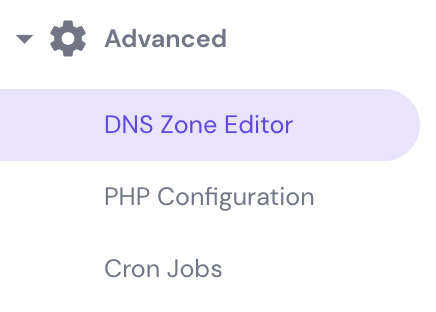
6. This will generate the TXT record value for the public key. Head to the DNS Zone Editor on your domain server to add the DNS records.
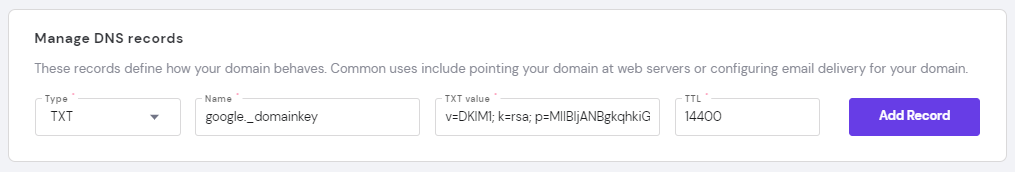
7. Add the record generated by Google under Manage DNS records. The receiving server can use this key to verify your messages.
8. Head back to the Google Workspace authentication page, then click on the START AUTHENTICATION button to turn on DKIM signing.
9. To verify that the DKIM security standard works, send an email message to someone who uses Gmail or Google Workspace.
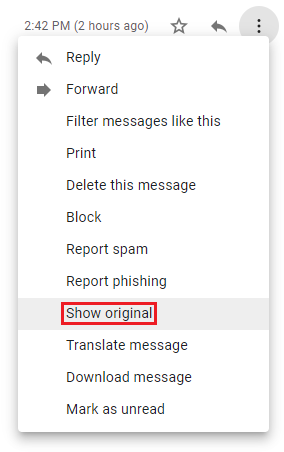
10. Access the receiving email’s inbox and open the message. Click on the three dots on the top left and select Show original.
11. If the DKIM is already working, then it will display PASS in front of your domain name, which means that the domain is secure.
Keep in mind that changes may take up to 24 hours to propagate.
Adding DKIM Records When Running a Private Mail Server
A DKIM generator, such as SparkPost, is needed to generate the keys for the signature when you’re running your own mail server. Some generators give you the option to create your selector, and others will make it for you.
- Once the keys have been generated, copy the public DKIM key and add it to the DNS records. Select TXT for the type, and the name will follow this format:
Selector-name._domainkey - Paste the public DKIM key in the Target or Content section. For the private key, ensure that the email server supports DKIM.
- Create a new text file with the private key. Make sure to copy everything from BEGIN RSA PRIVATE KEY to END RSA PRIVATE KEY.
- Save the file to C:\pmta on Windows or /etc/pmta on Linux.
- Go to the domain’s control panel and select the text file under DKIM signing.
- Lastly, add the selector name there to finalize the DKIM signature process.
Conclusion
To prevent the delivery of harmful emails or spoofing, it is your responsibility to protect all messages from the domain. This is especially true for small businesses, as marketing emails don’t want to end up in the spam or junk folder.
One of the solutions to this problem is adding a DKIM record and signature. The email servers of the sender and receiver will authenticate your messages using private-public DKIM keys. The DKIM standard will also improve email deliverability and work well with SPF and DMARC.
We have shown you the different ways to add a DKIM record and signature. Adding DKIM records can be done using Hostinger’s email service, Google Workspace, and with a private mail server. Whichever method you choose, make sure to get the private-public DKIM keys first.
Now you can easily secure every message you send from your domain. Good luck.





Comments
October 23 2020
Hi, all emails sent from Hostinger sign DKIM? Or do i need something in particular?
February 02 2021
Hi there, Ariel! For shared and cloud plans, you should enable DKIM as shown in this article ;)
January 26 2022
Hi; A complete beginner here, It was very helpful but i have a question. I've followed all the steps to set up the DKIM record using google workspace, it is still authenticating after 24 hs, not green light yet. I realized that in my DNS Zone Editor there are some CNAME records such as "autodiscover.mail.hostinger.com" and "autoconfig.mail.hostinger.com" not sure if those were there for people who use the mail option that is free for the 1st hosting year, but I won't use that service cause I use G suite. Should I delete those CNAME records? Will those cause any issue with my dkim certificate or mails? Thanks
February 04 2022
Hi Gabriel ;) Yes, those CNAME records are used by default Hostinger email. If you're using Google Workspace, feel free to remove it. As for the DKIM, I would suggest to double check if it's being discovered worldwide: https://dnschecker.org/ (where domain name is, enter google._domainkey.yourdomain.tld and select TXT). If it's not propagating, that means there's an issue with your DNS record, so I'd suggest to get in touch with our Customer Success team. If it is propagating well, then there might be an issue on Google's end, so I'd recommend getting in touch with their support team. Good luck!
July 23 2023
Hi Admin I've generated new DKIM manually through Custom DKIM menu (at tne navigator bar of Email dashboard). And current status is waiting for verification (take 8 hr) Questtion : Can I cancel it this verification process by deleting new DKIM ?
July 28 2023
Hey! If you wish to cancel the DKIM record, you would need to remove it, however this will still need time to update due to DNS propagation, when updating DNS recomrds (both adding and remocing) triggers the propagation, and it can take up to 24 hours for the DNS records to fully update.